Securing Internet of Things (IoT) Devices in Enterprise Networks
Saheed Abiodun Adebayo (Saint Louis University), Victor Owolabi (Saint Louis University), Dr. Maria Weber (Saint Louis University)
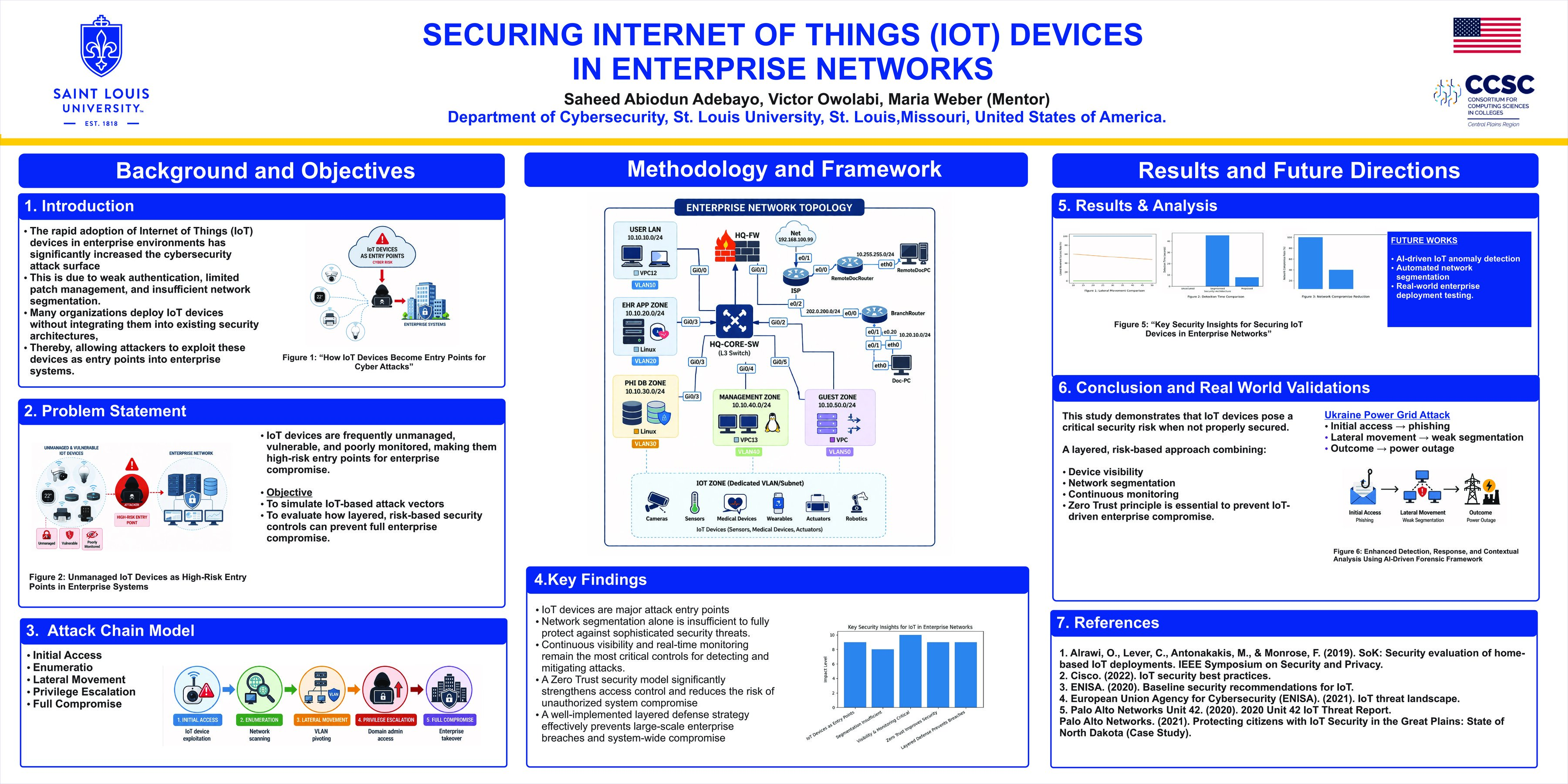
The rapid adoption of Internet of Things (IoT) devices in enterprise environments has significantly increased the cybersecurity attack surface due to the weak authentication mechanisms, limited patch management, and insufficient network segmentation. Many organizations deploy IoT devices without fully integrating them into existing security architectures, which serves as entry points for attackers to exploit the critical systems. This research project investigates how insecure IoT devices can be leveraged to compromise an enterprise network and demonstrates the importance of layered, risk-based security controls for mitigating such threats. The study was conducted in a controlled virtual environment designed to simulate a realistic enterprise network infrastructure. The virtual lab included an IoT device, user workstations, servers, and domain services, which are configured within an isolated network. The experiment demonstrated a full attack chain in which an attacker first gained initial access through a vulnerable IoT device, then performed network enumeration, lateral movement, and privilege escalation to obtain administrative control over the enterprise domain. Tools commonly used in penetration testing and network analysis were utilized to observe attacker behavior and to evaluate how insufficient segmentation and monitoring can allow the compromise to spread across the network. Through this simulation, the research highlights how IoT devices can serve as high-risk entry points when they are not properly secured or monitored. The results show that traditional endpoint-focused security measures are not sufficient for protecting heterogeneous environments that include unmanaged or resource-constrained devices. The study emphasizes the importance of device visibility, network segmentation, least-privilege access, continuous monitoring, and defense-in-depth architecture in preventing IoT-based attack vectors from escalating into full network compromise.