Post-Quantum Cryptography Adoption in Open-Source Software: An Empirical Study
Lukas Mehl (Washburn University)
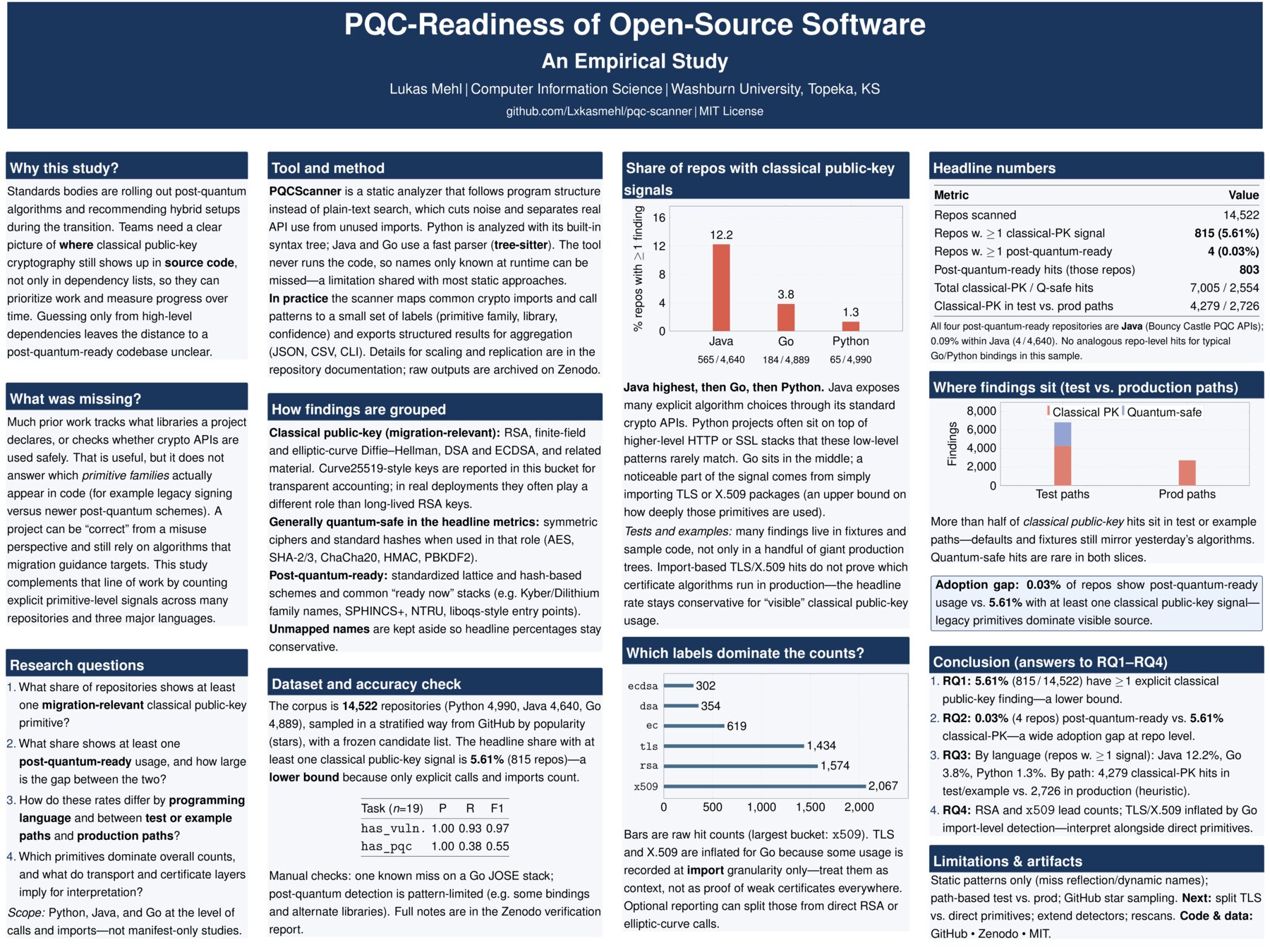
In 2024, NIST finalized the world’s first post-quantum cryptography standards, marking the beginning of a global cryptographic transition. But how much of the open-source ecosystem is actually making the switch? To answer this, I built PQCScanner, a static analysis tool that scans Python, Java, and Go repositories for cryptographic API usage and classifies each finding as post-quantum-vulnerable, quantum-safe, or PQC-ready. I then applied it to a stratified sample of approximately 14,500 public GitHub repositories. The answer is striking: only 4 repositories in the entire sample (0.03%) show any evidence of PQC-ready cryptography. Meanwhile, 5.61% actively use primitives that a sufficiently powerful quantum computer could break, with Java projects nearly ten times more exposed than Python ones (12.2% vs. 1.3%). These findings suggest that despite finalized standards, real-world migration has not meaningfully begun. The tools exist, the standards are ready, but the code has not caught up. Like all static analysis approaches, PQCScanner has limitations. Detection is based on imports and direct API calls, meaning indirect or runtime-configured cryptography may go undetected. Import-level signals such as TLS and X.509 usage are also included as vulnerability indicators, which may overestimate exposure in some cases. A manual precision and recall evaluation on a subset of files is underway to quantify these effects. PQCScanner and the full dataset are publicly available, enabling future work to track whether and how fast this changes.